PT0-002 / Modul 01: Festlegung der organisatorischen/Kundenanforderungen für Penetrationstests
1. Einleitung
Penetrationstests (PenTest) sind eine wichtige Methode zur Bewertung und Verbesserung der Cybersicherheitslage eines Unternehmens. In diesem Kapitel werden der PenTest-Prozess, die Compliance-Anforderungen und Möglichkeiten zur Wahrung der Professionalität während des Testprozesses vorgestellt.
Die Festlegung der organisatorischen/Kundenanforderungen für Penetrationstests ist aus mehreren wichtigen Gründen ein entscheidender Schritt im Prozess:
1. Klare Ziele definieren: Die Festlegung des Umfangs hilft dabei, klare, spezifische Ziele für den Penetrationstest festzulegen. Dadurch wird sichergestellt, dass der Test mit den Sicherheitszielen des Unternehmens übereinstimmt und seine dringendsten Anliegen berücksichtigt.
2. Ressourcenoptimierung: Durch eine klare Definition des Umfangs können Organisationen ihre Ressourcen effizienter zuweisen. So wird vermieden, dass Zeit und Aufwand für das Testen von Bereichen verschwendet werden, die für die Sicherheitslage der Organisation nicht kritisch oder relevant sind.
3. Risikomanagement: Eine angemessene Abgrenzung hilft dabei, die wichtigsten Assets und Systeme für den Test zu identifizieren und zu priorisieren. Dadurch wird sichergestellt, dass Hochrisikobereiche während des Penetrationstests die entsprechende Aufmerksamkeit und die erforderlichen Ressourcen erhalten.
4. Rechtliche und Compliance-Überlegungen: Durch die Festlegung des Umfangs wird sichergestellt, dass der Penetrationstest den relevanten Gesetzen, Vorschriften und Industriestandards entspricht. Dies kann dazu beitragen, unbeabsichtigte rechtliche Probleme zu vermeiden, die durch Tests über vereinbarte Grenzen hinaus entstehen können.
5. Minimieren von Betriebsunterbrechungen: Ein gut definierter Umfang kann das Risiko von Störungen des normalen Geschäftsbetriebs begrenzen. Er kann festlegen, welche Systeme getestet werden können, wann Tests stattfinden können und welche Arten von Tests zulässig sind.
6. Erwartungen festlegen: Die Festlegung des Umfangs legt klare Erwartungen sowohl für das Testteam als auch für den Kunden fest. Sie hilft, Missverständnisse darüber zu vermeiden, was getestet wird, wie es getestet wird und welche Ergebnisse zu erwarten sind.
7. Kostenkontrolle: Durch eine klare Definition des Umfangs können Unternehmen die mit Penetrationstests verbundenen Kosten besser einschätzen und kontrollieren. Dies verhindert eine Ausweitung des Umfangs und unerwartete Ausgaben.
8. Maßgeschneiderter Ansatz: Jede Organisation hat einzigartige Sicherheitsanforderungen. Durch die Festlegung des Umfangs kann ein maßgeschneiderter Ansatz entwickelt werden, der die spezifischen Anforderungen, Bedenken und Einschränkungen der Organisation berücksichtigt.
9. Ethische Überlegungen: Eine angemessene Festlegung des Umfangs stellt sicher, dass Penetrationstests ethisch und verantwortungsbewusst durchgeführt werden. Sie setzt Grenzen, die verhindern, dass Tester versehentlich auf vertrauliche Daten oder Systeme außerhalb des vereinbarten Umfangs zugreifen oder diese kompromittieren.
10. Messbare Ergebnisse: Ein klar definierter Umfang ermöglicht besser messbare und vergleichbare Ergebnisse. Dies ist besonders nützlich, um Sicherheitsverbesserungen im Laufe der Zeit zu verfolgen oder Ergebnisse verschiedener Penetrationstests zu vergleichen.
11. Einhaltung gesetzlicher Vorschriften: In Branchen, die besonderen Vorschriften unterliegen (z. B. Gesundheitswesen, Finanzen), wird durch die Festlegung des Umfangs sichergestellt, dass die Penetrationstests den gesetzlichen Anforderungen entsprechen und als Nachweis der Einhaltung verwendet werden können.
12. Erleichterung der Kommunikation: Ein klarer Umfang sorgt für ein gemeinsames Verständnis zwischen allen Beteiligten und erleichtert die Kommunikation während des gesamten Penetrationstestprozesses.
13. Konzentration auf den Geschäftskontext: Durch die Festlegung des Umfangs kann der Penetrationstest an den Geschäftskontext der Organisation angepasst werden. Dadurch wird sichergestellt, dass die Tests und Ergebnisse für die spezifische Branche, Größe und das Risikoprofil der Organisation relevant sind.
14. Vorbereitung auf die Behebung: Durch eine klare Definition der zu testenden Stoffe können sich Unternehmen besser auf mögliche Befunde vorbereiten und Ressourcen für Behebungsmaßnahmen effektiver zuweisen.
Zusammenfassend lässt sich sagen, dass die Festlegung der Anforderungen der Organisation/des Kunden an Penetrationstests unerlässlich ist, um sicherzustellen, dass die Tests effektiv, effizient, relevant und auf die Bedürfnisse und Einschränkungen der Organisation abgestimmt sind. Sie bildet die Grundlage für einen erfolgreichen Penetrationstest, der wertvolle Erkenntnisse und umsetzbare Ergebnisse zur Verbesserung der Sicherheitslage der Organisation liefert.
1. Vergleichen und kontrastieren Sie Governance-, Risiko- und Compliance-Berichte.
Erläuterung:
Governance-Berichte konzentrieren sich darauf, wie eine Organisation verwaltet und kontrolliert wird. Risikoberichte identifizieren und bewerten potenzielle Bedrohungen für eine Organisation. Compliance-Berichte belegen die Einhaltung von Gesetzen, Vorschriften und Branchenstandards.
Illustratives Szenario:
Eine multinationale Bank, GlobalFinance, führt jährliche Bewertungen durch:
- Governance-Bericht: Gibt einen Überblick über die Führungsstruktur, Entscheidungsprozesse und internen Kontrollen der Bank.
- Risikobericht: Identifiziert potenzielle Cyber-Bedrohungen, Marktrisiken und betriebliche Schwachstellen.
- Compliance-Bericht: Weist die Einhaltung von Vorschriften wie DSGVO, PCI DSS und lokalen Bankgesetzen nach.
Während der Governance-Bericht eine Verbesserung der Aufsicht des Vorstands über die Cybersicherheit empfehlen könnte, könnte der Risikobericht bestimmte Schwachstellen im Online-Banking-System hervorheben. Der Compliance-Bericht würde dann zeigen, ob diese Schwachstellen gegen gesetzliche Anforderungen verstoßen.
2. Die Bedeutung des Umfangs und der organisatorischen/Kundenanforderungen
Erläuterung:
Der Umfang definiert die Grenzen eines Penetrationstests und stellt sicher, dass die Testbemühungen zielgerichtet und effizient sind und den Anforderungen der Organisation entsprechen. Ein richtiger Umfang verhindert unnötige Arbeit, reduziert Risiken und stellt sicher, dass kritische Systeme gründlich untersucht werden.
Illustratives Szenario:
Das Softwareunternehmen TechInnovate fordert einen Penetrationstest für seine neue Cloud-basierte Anwendung an. Der Scoping-Prozess umfasst:
- Definieren von Testgrenzen (z. B. nur die Anwendung, nicht die zugrunde liegende Cloud-Infrastruktur)
- Identifizierung kritischer Assets (z. B. Benutzerdatenbank, Zahlungsabwicklungsmodul)
- Festlegen von Testbeschränkungen (z. B. keine Denial-of-Service-Angriffe)
- Abstimmung mit organisatorischen Vorgaben (z. B. Testen außerhalb der Stoßzeiten)
Durch diese Abgrenzung wird sichergestellt, dass sich der Penetrationstest auf die wichtigsten Anliegen von TechInnovate konzentriert und gleichzeitig Störungen des Geschäftsbetriebs vermieden werden.
3. Die Bedeutung der Kommunikation während des Penetrationstests
Erläuterung:
Eine effektive Kommunikation stellt sicher, dass alle Beteiligten den Fortschritt, die Ergebnisse und die Auswirkungen des Tests verstehen. Sie hilft dabei, Erwartungen zu steuern, ermöglicht eine schnelle Reaktion auf kritische Ergebnisse und stellt sicher, dass der Abschlussbericht den Anforderungen der Organisation entspricht.
Illustratives Szenario:
Während eines Penetrationstests für SecureHealth, einen Gesundheitsdienstleister, entdeckt das Testteam eine kritische Schwachstelle im Patientendatensystem. Sie teilen dies dem IT-Team des Kunden umgehend mit, damit eine sofortige Schadensbegrenzung möglich ist. Während des gesamten Tests stellen sie tägliche Updates und eine Zwischenbesprechung bereit, um sicherzustellen, dass das Management von SecureHealth umfassend informiert ist und rechtzeitig Entscheidungen über die Ressourcenzuweisung und das Risikomanagement treffen kann.
4. Zeigen Sie in einem Szenario eine ethische Hackermentalität, indem Sie Professionalität und Integrität wahren
Erläuterung:
Eine ethische Hackermentalität beinhaltet das Durchführen von Tests mit Erlaubnis, das Respektieren von Grenzen, den Schutz vertraulicher Daten und die Priorisierung der Sicherheit des Kunden. Es erfordert die Wahrung von Professionalität und Integrität während des gesamten Testprozesses.
Illustratives Szenario:
Während eines Penetrationstests für EduOnline, eine E-Learning-Plattform, erhält das Testteam Zugriff auf eine Datenbank mit Studenteninformationen. Anstatt diese Daten zu exfiltrieren, dokumentieren sie die Schwachstelle, informieren den Kunden umgehend und geben Empfehlungen zur Sicherung der Datenbank. Sie stellen außerdem sicher, dass alle Testdaten nach dem Einsatz sicher gelöscht werden, und demonstrieren damit ihr Engagement für ethische Praktiken und Datenschutz.
5. Führen Sie in einem gegebenen Szenario eine passive Aufklärung durch
Erläuterung:
Bei der passiven Aufklärung werden Informationen über ein Ziel gesammelt, ohne direkt mit dessen Systemen zu interagieren. Dies kann die Nutzung öffentlicher Quellen, sozialer Medien und anderer frei verfügbarer Informationen umfassen.
Illustratives Szenario:
Vor dem Beginn eines autorisierten Penetrationstests für GreenEnergy, ein Unternehmen für erneuerbare Energien, führt das Testteam eine passive Aufklärung durch:
– Sie analysieren die Website von GreenEnergy und achten auf die verwendeten Technologien und potenziellen Einstiegspunkte.
– Sie prüfen die Stellenausschreibungen des Unternehmens, um sich über deren Technologie-Stack zu informieren.
– Sie untersuchen öffentliche Aufzeichnungen und Pressemitteilungen auf Informationen zur Infrastruktur von GreenEnergy.
– Sie verwenden OSINT-Tools, um Informationen über die Netzwerkbereiche und E-Mail-Formate des Unternehmens zu sammeln.
Diese passive Aufklärung liefert wertvolle Informationen für die nachfolgenden Phasen des Penetrationstests – und das, ohne die Sicherheitssysteme von GreenEnergy zu alarmieren oder eine direkte Interaktion mit deren Netzwerk zu erfordern.
Zusammengenommen stellen diese Ziele sicher, dass Penetrationstester ihre Arbeit methodisch, ethisch und im Einklang mit den Anforderungen des Kunden und den gesetzlichen Anforderungen angehen. Sie betonen die Bedeutung klarer Kommunikation, professionellen Verhaltens und gründlicher Vorbereitung im Penetrationstestprozess.
2. Definition von organisatorischem PenTesting
2.1 Bewertung der Cyber-Gesundheit und -Resilienz
Organisationen erkennen zunehmend die Notwendigkeit, ihre Systeme zu sichern. Um die Vertraulichkeit, Integrität und Verfügbarkeit (CIA) von Daten zu gewährleisten, setzen viele drei Hauptkontrollarten ein:
a) Administrative Kontrollen: Hierzu gehören Richtlinien und Verfahren. Beispielsweise Kennwortrichtlinien, die komplexe Kennwörter und deren regelmäßige Änderungen vorschreiben, oder Nutzungsrichtlinien, die festlegen, wie Mitarbeiter Unternehmensressourcen nutzen dürfen.
b) Physische Kontrollen: Diese beziehen sich auf den Schutz physischer Vermögenswerte. Beispiele hierfür sind verschlossene Serverräume, Überwachungskameras und biometrische Zugangssysteme.
c) Technische oder logische Kontrollen: Diese umfassen Software- und Hardwarelösungen wie Firewalls, Verschlüsselung und Angriffserkennungssysteme.
Alle diese Kontrollen sollten dem Prinzip der geringsten Privilegien entsprechen. Dies bedeutet, dass den Benutzern nur die Mindestzugriffsrechte gewährt werden, die sie zur Ausführung ihrer Aufgaben benötigen. Dieses Prinzip trägt dazu bei, den potenziellen Schaden durch Unfälle oder böswillige Handlungen zu minimieren.
2.2 Reduzierung des Gesamtrisikos
Ein Hauptziel von PenTesting ist die Reduzierung des Gesamtrisikos. Die Formel zur Risikobestimmung lautet:
RISIKO = BEDROHUNG * VERWUNDBARKEIT
Wo:
– Bedrohungen können Schadsoftware, Hacker oder sogar Naturkatastrophen sein.
- Schwachstellen sind Schwächen oder Mängel im System, die ausgenutzt werden könnten.
Wenn ein Server beispielsweise eine ungepatchte Sicherheitslücke aufweist (Schweregrad 8 von 10) und die Gefahr einer Ausnutzung mäßig ist (5 von 10), beträgt das Risiko 8 * 5 = 40 von 100.
Zum Risikomanagement gehört das Identifizieren, Bewerten, Analysieren und Reagieren auf diese Risiken. PenTesting hilft bei diesem Prozess, indem es Schwachstellen aufdeckt, bevor böswillige Akteure sie ausnutzen können.
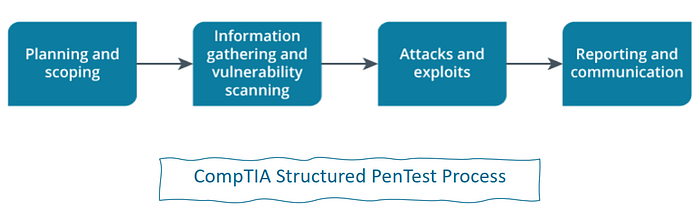
2.3 Der strukturierte PenTest-Prozess von CompTIA
CompTIA beschreibt einen achtstufigen Prozess zur Durchführung von Penetrationstests:
1. Planung und Umfang: Hierzu gehört die Skizzierung des Plans für den PenTest, einschließlich der Definition der Ziele, der zu testenden Systeme und der Einschränkungen.
2. Aufklärung: Sammeln von Informationen über das Ziel. Dabei kann es sich sowohl um passive (öffentlich verfügbare Informationen) als auch um aktive (direkte Interaktion mit dem Ziel) Methoden handeln.
3. Scannen: Identifizieren von aktiven Hosts, offenen Ports und laufenden Diensten. In dieser Phase werden häufig Tools wie Nmap verwendet.
4. Zugriff erlangen: Versuch, Schwachstellen auszunutzen, um zu sehen, wie tief der Tester in das Netzwerk eindringen kann.
5. Aufrechterhaltung des Zugriffs: Sobald der Zugriff erlangt wurde, versucht der Tester, ihn so lange wie möglich unentdeckt zu halten und simuliert so das Verhalten eines echten Angreifers.
6. Spuren verwischen: Entfernen Sie alle Beweise für den Einbruch, wie etwa Protokolleinträge oder erstellte Dateien.
7. Analyse: Analysieren der Ergebnisse und Ableiten einer Zusammenfassung der Risikobewertung für jede gefundene Schwachstelle.
8. Berichterstattung: Bereitstellung der Ergebnisse in einem umfassenden Bericht, häufig einschließlich einer Zusammenfassung und detaillierter technischer Ergebnisse.
Szenario: PenTest von MediTech-Gesundheitssystemen
MediTech ist ein regionaler Gesundheitsdienstleister mit mehreren Kliniken und einem Zentralkrankenhaus. Das Unternehmen hat CyberShield, ein renommiertes Unternehmen für Cybersicherheit, beauftragt, einen umfassenden Penetrationstest seiner Systeme durchzuführen.
1. Planung und Umfang: CyberShield trifft sich mit den IT- und Managementteams von MediTech, um den PenTest-Plan zu skizzieren. Sie definieren Ziele (Bewertung der Sicherheit von Patientenakten und des Terminsystems), zu testende Systeme (Hauptkrankenhausnetzwerk, Kliniknetzwerke und Patientenportal) und Einschränkungen (keine Unterbrechung kritischer medizinischer Systeme).
2. Aufklärung: CyberShield beginnt, Informationen über MediTech zu sammeln:
- Passiv: Sie durchsuchen öffentliche Aufzeichnungen, analysieren die Website von MediTech und überprüfen die Social-Media-Profile der Mitarbeiter.
- Aktiv: Sie rufen MediTech an und geben sich als potenzielle Patienten aus, um Informationen über deren Systeme zu sammeln.
3. Scannen: Mithilfe von Nmap und anderen Tools scannt CyberShield die Netzwerke von MediTech:
- Sie identifizieren Live-Hosts in den Netzwerken der Krankenhäuser und Kliniken.
- Sie entdecken offene Ports auf verschiedenen Servern, darunter auch einige unerwartete offene Ports auf dem Server des Patientenportals.
- Sie listen laufende Dienste auf und stellen fest, dass auf einem der Klinikserver eine veraltete Version eines Datenbankdienstes vorhanden ist.
4. Zugriff erlangen: CyberShield versucht, die gefundenen Schwachstellen auszunutzen:
- Sie nutzen einen bekannten Exploit des veralteten Datenbankdienstes, um sich erstmals Zugriff auf einen Klinikserver zu verschaffen.
- Von dort aus nutzen sie ein schwaches Kennwort eines Administratorkontos, um auf das Hauptnetzwerk des Krankenhauses zuzugreifen.
5. Zugriff aufrechterhalten: Sobald CyberShield in die Systeme von MediTech eingedrungen ist:
- Erstellt ein verstecktes Benutzerkonto mit erhöhten Rechten.
- Installiert ein getarntes Remote-Zugriffstool auf mehreren wichtigen Servern.
- Richtet geplante Aufgaben ein, die sich regelmäßig bei ihrem Befehls- und Kontrollserver anmelden.
6. Spuren verwischen: Um unentdeckt zu bleiben, bietet CyberShield:
- Ändert Systemprotokolle, um Beweise für ihr Eindringen zu entfernen.
- Löscht alle während ihrer Aktivitäten erstellten temporären Dateien.
- Stellt sicher, dass das Remote-Zugriffstool nicht in der Liste der laufenden Prozesse angezeigt wird.
7. Analyse: CyberShield analysiert seine Ergebnisse:
- Sie identifizieren kritische Schwachstellen im Patientenportal und den Kliniknetzwerken.
- Sie beurteilen die potenziellen Auswirkungen jeder Schwachstelle und berücksichtigen dabei Faktoren wie die einfache Ausnutzung und die potenzielle Datengefährdung.
- Auf der Grundlage ihrer Analyse bewerten sie jede Schwachstelle auf einer Skala von gering bis kritisch.
8. Berichterstattung: CyberShield liefert MediTech einen umfassenden Bericht:
- Zusammenfassung: Allgemeiner Überblick über den Test, wichtige Ergebnisse und allgemeine Risikobewertung.
- Detaillierte technische Ergebnisse: Ausführliche Erklärung jeder Schwachstelle, einschließlich der Art und Weise, wie sie entdeckt und ausgenutzt wurde.
- Risikobewertungen: Klare Aufschlüsselung der Risikostufen für jede Schwachstelle.
- Empfehlungen: Konkrete, umsetzbare Schritte für MediTech zur Behebung jeder Schwachstelle.
- Anhänge: Rohdaten aus Scans, Screenshots erfolgreicher Exploits (mit redigierten vertraulichen Informationen) und andere unterstützende Beweise.
Dieses Szenario veranschaulicht, wie jeder Schritt des Penetrationstestprozesses in einem realen Kontext angewendet wird, und demonstriert den methodischen Ansatz, mit dem professionelle Pentester die Sicherheitslage eines Unternehmens gründlich beurteilen.
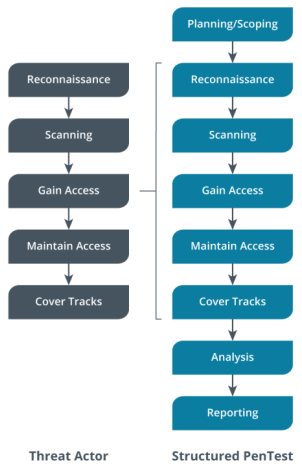
2.4 Vergleich der beim PenTesting durchgeführten Schritte
Es ist wichtig, zwischen PenTesting-Teams und tatsächlichen Bedrohungsakteuren zu unterscheiden:
- PenTesting-Team: Das Hauptziel besteht darin, die Abwehrmechanismen einer Infrastruktur zu testen. Sie agieren innerhalb vereinbarter Grenzen und mit der Erlaubnis der Organisation.
- Bedrohungsakteure: Das Hauptziel besteht darin, die Integrität des Systems zu böswilligen Zwecken zu verändern. Sie kennen keine Grenzen und zielen oft darauf ab, Schaden anzurichten oder Informationen zu stehlen.
Das Verständnis dieses Unterschieds hilft dabei, reale Angriffe zu simulieren und gleichzeitig ethische und rechtliche Grenzen einzuhalten.
Szenario: SecureBanks Online-Banking-Plattform
SecureBank hat kürzlich seine Online-Banking-Plattform aktualisiert und möchte deren Sicherheit gewährleisten. Sie beauftragt ein PenTesting-Team mit einer Sicherheitsbewertung. Inzwischen hat eine Gruppe von Bedrohungsakteuren, ohne dass SecureBank davon weiß, ebenfalls ein Auge auf die Systeme der Bank geworfen.
PenTesting-Team:
1. Engagement: Das Team wird offiziell von SecureBank eingestellt und unterzeichnet einen Vertrag, in dem Umfang und Grenzen seiner Arbeit dargelegt werden.
2. Ziele: Ihr Ziel ist es, Schwachstellen in der Online-Banking-Plattform zu identifizieren, um SecureBank dabei zu helfen, seine Sicherheit zu verbessern.
3. Methodik: Sie verfolgen einen strukturierten Ansatz, beginnend mit Aufklärung und Scannen, und versuchen dann, entdeckte Schwachstellen auszunutzen.
4. Einschränkungen: Sie arbeiten innerhalb vereinbarter Grenzen. Beispielsweise vermeiden sie möglicherweise Tests während der Stoßzeiten, um Störungen für die Kunden zu vermeiden.
5. Ethik: Wenn sie Zugriff auf sensible Daten erhalten, exfiltrieren oder missbrauchen sie diese nicht.
6. Kommunikation: Sie halten regelmäßigen Kontakt mit dem IT-Team von SecureBank, insbesondere wenn sie kritische Schwachstellen entdecken.
7. Dauer: Ihr Engagement hat einen festgelegten Zeitrahmen, in der Regel einige Wochen.
8. Berichterstattung: Am Ende des Tests übermitteln Sie SecureBank einen detaillierten Bericht über Ihre Ergebnisse und Empfehlungen.
Bedrohungsakteur:
1. Engagement: Sie sind nicht autorisiert und operieren illegal, oft von einem entfernten Standort aus.
2. Ziele: Ihr Ziel ist typischerweise finanzieller Gewinn, entweder durch den direkten Diebstahl von Geldern oder den Verkauf gestohlener Daten im Dark Web.
3. Methodik: Sie verwenden zwar möglicherweise ähnliche Tools und Techniken wie das PenTesting-Team, sind jedoch an keine Regeln oder ethischen Grundsätze gebunden.
4. Einschränkungen: Sie haben keine Einschränkungen und können jederzeit angreifen, auch während der Stoßzeiten, um maximale Verwirrung zu stiften.
5. Ethik: Wenn sie Zugriff auf sensible Daten erhalten, werden sie diese für persönliche Zwecke nutzen oder verkaufen.
6. Kommunikation: Sie vermeiden jegliche Kommunikation mit SecureBank und versuchen, so lange wie möglich unentdeckt zu bleiben.
7. Dauer: Sie können unentdeckt monate- oder sogar jahrelang im System verbleiben.
8. Meldung: Anstelle einer Meldung hinterlassen sie möglicherweise eine Lösegeldforderung, wenn sie sich für den Einsatz von Ransomware entscheiden, oder verschwinden einfach mit den gestohlenen Daten.
Beispielergebnis:
PenTesting-Team: Sie entdecken eine Schwachstelle in der Funktion zum Zurücksetzen des Passworts, die eine Kontoübernahme ermöglichen könnte. Sie benachrichtigen SecureBank umgehend, demonstrieren die Schwachstelle in einer kontrollierten Umgebung und geben Empfehlungen zur Behebung. SecureBank behebt die Schwachstelle innerhalb weniger Tage.
Bedrohungsakteur: Sie entdecken dieselbe Schwachstelle, nutzen sie aber aus, um Zugriff auf mehrere Kundenkonten zu erhalten. Sie überweisen Geld auf nicht nachverfolgbare Konten und verkaufen Kundendaten im Dark Web. SecureBank entdeckt den Verstoß erst Monate später, wenn Kunden nicht autorisierte Transaktionen melden.
Dieses Beispiel veranschaulicht den starken Kontrast zwischen PenTesting-Teams und Bedrohungsakteuren. Obwohl beide ähnliche Techniken verwenden, sind ihre Absichten, Methoden und Ergebnisse grundlegend unterschiedlich. PenTesting-Teams arbeiten mit dem Wissen und der Zustimmung der Organisation an der Verbesserung der Sicherheit, während Bedrohungsakteure versuchen, Schwachstellen ohne das Wissen der Organisation für böswillige Zwecke auszunutzen.
3. Compliance-Anforderungen
3.1 PCI DSS (Datensicherheitsstandard der Zahlungskartenindustrie)
PCI DSS legt Kontrollen fest, die für den Umgang mit Kreditkartendaten vorhanden sein müssen. Zu den wichtigsten Anforderungen gehören:
- Erstellen und Aufrechterhalten einer sicheren Netzwerkinfrastruktur: Dazu gehört die Implementierung von Firewalls und einer geeigneten Netzwerksegmentierung.
- Schutz der Karteninhaberdaten: Verwendung von Verschlüsselung bei der Datenübertragung und -speicherung.
- Pflege eines Schwachstellenmanagementprogramms: Regelmäßige Updates und Patches für Systeme.
- Implementierung strenger Zugriffskontrollmaßnahmen: Verwendung einer Multi-Faktor-Authentifizierung und des Prinzips der geringsten Privilegien.
- Regelmäßige Überwachung und Prüfung von Netzwerken: Durchführung regelmäßiger Sicherheitsscans und Penetrationstests.
- Aufrechterhalten einer Informationssicherheitsrichtlinie: Dokumentieren und Durchsetzen von Sicherheitspraktiken in der gesamten Organisation.
Unternehmen müssen bei der Sicherung ihrer Daten wachsam sein:
– Sie müssen Beurteilungen durchführen und die Ergebnisse melden.
– Die Händlerebene legt fest, ob ein Report on Compliance (ROC) ausgefüllt werden muss.
- Händler der Stufe 1 (die jährlich über 6 Millionen Kartentransaktionen abwickeln) müssen sich einer externen Prüfung durch einen zugelassenen Qualified Security Assessor (QSA) unterziehen.
– Die Stufen 1 und 2 müssen einen Konformitätsbericht ausfüllen.
- Die Stufen 2–4 können entweder einen externen Prüfer hinzuziehen oder einen Fragebogen zur Selbsteinschätzung (SAQ) einreichen, der belegt, dass sie aktive Schritte zur Sicherung der Infrastruktur unternehmen.
3.2 Datenschutz-Grundverordnung (DSGVO)
Der Schwerpunkt der DSGVO liegt auf dem Schutz von Verbraucherdaten:
- Es betrifft jeden, der Geschäfte mit Einwohnern der EU und Großbritanniens macht.
- Zu den Hauptkomponenten gehören:
a) Zustimmung erforderlich: Organisationen müssen für jede Datenquelle, die sie von Einzelpersonen sammeln, um Erlaubnis bitten.
b) Möglichkeit zum Widerruf der Einwilligung: Verbraucher können der Einwilligung jederzeit widersprechen.
c) Globale Reichweite: Gilt für alle Organisationen, die mit den Daten von EU-Bürgern umgehen, unabhängig davon, wo die Organisation ihren Sitz hat.
d) Einschränkung der Datenerfassung: Organisationen sollten nur das erfassen, was notwendig ist.
e) Meldung von Verstößen: Unternehmen müssen einen Verstoß innerhalb von 72 Stunden nach Entdeckung melden.
3.3 Weitere Datenschutzgesetze
- SHIELD Act (Stop Hacks and Improve Electronic Data Security): Erlassen im Bundesstaat New York zum Schutz der Daten der Bürger. Es verpflichtet Unternehmen, Schutzmaßnahmen für die „privaten Informationen“ der Einwohner New Yorks zu ergreifen.
- California Consumer Privacy Act (CCPA): Dieses Gesetz gibt den Einwohnern Kaliforniens mehr Kontrolle über ihre persönlichen Daten, einschließlich des Rechts zu erfahren, welche Daten gesammelt werden, und der Möglichkeit, deren Löschung zu verlangen.
- Health Insurance Portability and Accountability Act (HIPAA): Dieses US-Gesetz enthält Datenschutz- und Sicherheitsbestimmungen zum Schutz medizinischer Informationen. Es gilt für Gesundheitsdienstleister, Krankenversicherungen und Clearingstellen im Gesundheitswesen.
Beispiele für Unternehmen oder Organisationen, die PCI DSS, DSGVO, SHIELD Act, CCPA und HIPAA anwenden müssen, zusammen mit spezifischen Anwendungsfällen und den Vorteilen der Compliance.
1. PCI DSS (Datensicherheitsstandard der Zahlungskartenindustrie)
Beispielorganisation: Global Retail Inc., ein internationales E-Commerce-Unternehmen
Anwendungsfall: Global Retail wickelt über seinen Online-Shop und seine physischen Standorte weltweit jährlich Millionen von Kreditkartentransaktionen ab.
Anwendung: Sie müssen PCI-DSS-Standards in allen ihren Zahlungssystemen implementieren, darunter:
- Verschlüsselung von Karteninhaberdaten während der Übertragung und Speicherung
- Regelmäßiges Aktualisieren und Patchen von Systemen
- Implementierung strenger Zugriffskontrollen
- Durchführung regelmäßiger Sicherheitsbewertungen
Vorteile:
- Reduziertes Risiko von Datenschutzverletzungen und damit verbundenen Kosten
- Erhöhtes Kundenvertrauen und Loyalität
- Vermeidung hoher Bußgelder und Strafen durch Kartenmarken
- Verbesserte allgemeine Sicherheitslage
2. DSGVO (Datenschutz-Grundverordnung)
Beispielorganisation: EuroTech Solutions, ein Softwareunternehmen mit Sitz in den USA und Kunden in der EU
Anwendungsfall: EuroTech sammelt und verarbeitet personenbezogene Daten von EU-Bürgern für seine CRM- und Marketingaktivitäten.
Anwendung: Sie müssen:
- Holen Sie eine ausdrückliche Zustimmung zur Datenerfassung ein
- Bieten Sie Benutzern die Möglichkeit, auf ihre Daten zuzugreifen, diese zu ändern oder zu löschen.
- Datenschutzmaßnahmen umsetzen
- Ernennung eines Datenschutzbeauftragten
Vorteile:
- Verbessertes Vertrauen bei europäischen Kunden und Partnern
- Verbesserte Datenverwaltungspraktiken
- Vermeidung empfindlicher DSGVO-Bußgelder (bis zu 4 % des weltweiten Jahresumsatzes)
- Wettbewerbsvorteile in datenschutzbewussten Märkten
3. SHIELD Act (Gesetz zum Stoppen von Hacks und Verbessern der elektronischen Datensicherheit)
Beispielorganisation: NY Financial Advisors, ein kleines Finanzberatungsunternehmen in New York
Anwendungsfall: Das Unternehmen verarbeitet vertrauliche Finanzinformationen von Einwohnern New Yorks.
Anwendung: Sie müssen:
- Implementieren Sie ein Datensicherheitsprogramm
- Schulen Sie Ihre Mitarbeiter in Cybersicherheitspraktiken
- Führen Sie regelmäßige Risikobewertungen durch
- Stellen Sie sicher, dass Drittanbieter Daten schützen können
Vorteile:
- Reduziertes Risiko von Datenschutzverletzungen
- Verbessertes Kundenvertrauen
- Einhaltung der Gesetze des Staates New York
- Verbesserte allgemeine Sicherheitspraktiken
4. CCPA (California Consumer Privacy Act)
Beispielorganisation: TechGiant Corp, ein großes Technologieunternehmen mit Sitz in Kalifornien
Anwendungsfall: TechGiant sammelt und verarbeitet über seine verschiedenen Onlinedienste personenbezogene Daten von Einwohnern Kaliforniens.
Anwendung: Sie müssen:
- Bereitstellung klarer Informationen zu Datenerfassungspraktiken
- Opt-out-Optionen für Datenverkäufe anbieten
- Reagieren Sie auf Anfragen von Verbrauchern zum Zugriff auf oder zur Löschung von Daten
- Implementieren Sie angemessene Sicherheitsmaßnahmen
Vorteile:
- Mehr Transparenz und Vertrauen bei den kalifornischen Verbrauchern
- Verbessertes Datenmanagement und -organisation
- Vermeidung von CCPA-Strafen
- Vorbereitung auf mögliche Bundesdatenschutzgesetze
5. HIPAA (Health Insurance Portability and Accountability Act)
Beispielorganisation: HealthCare Plus, ein in mehreren Bundesstaaten tätiger Gesundheitsdienstleister
Anwendungsfall: HealthCare Plus verwaltet elektronische Gesundheitsakten und kommuniziert elektronisch mit Patienten und anderen Anbietern.
Anwendung: Sie müssen:
- Implementieren Sie strenge Zugriffskontrollen und Authentifizierung
- Verschlüsseln Sie Patientendaten während der Übertragung und im Ruhezustand
- Führen Sie regelmäßige Sicherheitsrisikobewertungen durch
- Schulen Sie Ihr Personal in Datenschutz- und Sicherheitspraktiken
- Schließen Sie Geschäftspartnervereinbarungen mit Lieferanten ab
Vorteile:
- Schutz sensibler Patienteninformationen
- Erhöhtes Patientenvertrauen und höhere Zufriedenheit
- Vermeidung schwerer HIPAA-Strafen
- Verbesserte Betriebseffizienz durch standardisierte Vorgehensweisen
In all diesen Fällen hilft Compliance Unternehmen nicht nur, Strafen zu vermeiden, sondern verbessert auch ihre allgemeine Sicherheitslage, schafft Vertrauen bei Kunden und führt oft zu verbesserten Betriebsabläufen. Während die anfängliche Implementierung schwierig und potenziell kostspielig sein kann, überwiegen die langfristigen Vorteile in Bezug auf Risikominderung und Reputationsverbesserung in der Regel die Kosten.
4. Vergleich von Standards und Methoden
4.1 Pentesting-Frameworks identifizieren
Penetration Testing Frameworks sind strukturierte Richtlinien und Methoden, die Sicherheitsexperten dabei helfen, gründliche und konsistente Sicherheitsbewertungen durchzuführen. Diese Frameworks bieten einen systematischen Ansatz zur Identifizierung von Schwachstellen, zur Ausnutzung von Schwächen und zur standardisierten Berichterstattung von Ergebnissen.
1. OWASP (Open Web Application Security Project)
OWASP ist eine gemeinnützige Stiftung, die sich für die Verbesserung der Softwaresicherheit einsetzt. Sie bietet verschiedene Ressourcen, Tools und Methoden für die Sicherheit von Webanwendungen.
Schlüsselkomponenten:
- OWASP Top 10: Eine regelmäßig aktualisierte Liste der kritischsten Sicherheitsrisiken für Webanwendungen
- OWASP-Testhandbuch: Ein umfassender Leitfaden zum Testen der Sicherheit von Webanwendungen
- OWASP ZAP (Zed Attack Proxy): Ein Open-Source-Sicherheitsscanner für Webanwendungen
Anwendungsbeispiel: Ein Startup für Finanztechnologie entwickelt eine neue Online-Banking-Plattform. Dabei verwendet es die OWASP Top 10 als Checkliste, um sicherzustellen, dass es die kritischsten Sicherheitsrisiken berücksichtigt. Während der Entwicklung scannt es seine Anwendung regelmäßig mit OWASP ZAP, um potenzielle Schwachstellen zu identifizieren. Vor der Markteinführung führt es eine gründliche Bewertung gemäß dem OWASP Testing Guide durch, um eine umfassende Sicherheitsabdeckung sicherzustellen.
2. NIST (Nationales Institut für Standards und Technologie)
NIST ist eine US-Regierungsbehörde, die Standards und Richtlinien für die Cybersicherheit entwickelt. Obwohl es sich nicht speziell um ein Pentesting-Framework handelt, bietet NIST wertvolle Ressourcen für Sicherheitstests.
Schlüsselkomponenten:
- NIST SP 800–115: Technischer Leitfaden zum Testen und Bewerten der Informationssicherheit
- NIST Cybersecurity Framework: Bietet eine Reihe von Richtlinien zur Minderung organisatorischer Cybersicherheitsrisiken
Anwendungsbeispiel: Ein großer Regierungsauftragnehmer bereitet sich auf ein Sicherheitsaudit vor. Er verwendet NIST SP 800–115 als Leitfaden für seinen internen Sicherheitsbewertungsprozess und stellt sicher, dass alle Aspekte seiner Informationssysteme abgedeckt sind. Außerdem richtet er seine allgemeine Sicherheitsstrategie am NIST Cybersecurity Framework aus und verwendet dessen fünf Kernfunktionen (Identifizieren, Schützen, Erkennen, Reagieren, Wiederherstellen), um sein Sicherheitsprogramm zu strukturieren.
3. OSSTMM (Handbuch zur Open Source-Sicherheitstestmethodik)
OSSTMM ist eine von Experten überprüfte Methode zur Durchführung von Sicherheitstests und -metriken. Sie bietet einen wissenschaftlichen Ansatz zum Testen der Betriebssicherheit physischer Standorte, menschlicher Interaktionen und aller Formen der Kommunikation.
Schlüsselkomponenten:
- Sechs Abschnitte, die unterschiedliche Arten der Sicherheit abdecken (physisch, Spektrum, Kommunikation, Datennetzwerke, Umwelt und Mensch)
- RAV (Risk Assessment Values): Ein quantitativer Ansatz zur Messung der Sicherheit
Anwendungsbeispiel: Ein multinationaler Konzern möchte die Sicherheit seines gesamten Betriebs bewerten, einschließlich physischer Büros, digitaler Infrastruktur und menschlicher Faktoren. Er verwendet OSSTMM als umfassendes Framework für diese Bewertung. Zum Beispiel:
- Physische Sicherheit: Sie testen Zugangskontrollen, Überwachungssysteme und Alarmreaktionen.
- Datennetzwerke: Sie führen gründliche Netzwerkpenetrationstests durch.
- Menschlich: Sie führen Social-Engineering-Tests durch, um das Sicherheitsbewusstsein der Mitarbeiter zu bewerten. Nach der Bewertung verwenden sie das RAV-System von OSSTMM, um ihre aktuelle Sicherheitslage zu quantifizieren und Verbesserungen im Laufe der Zeit zu verfolgen.
Vergleichende Anwendung von Frameworks:
Betrachten wir ein Szenario, in dem ein großes E-Commerce-Unternehmen eine umfassende Sicherheitsbewertung durchführen möchte:
1. OWASP: Sie würden dies hauptsächlich für ihre Webanwendungen und APIs verwenden. Das Sicherheitsteam würde:
o Ziehen Sie die OWASP Top 10 zu Rate, um Ihre Testbemühungen zu priorisieren.
o Verwenden Sie den OWASP-Testleitfaden, um eine umfassende Abdeckung der Sicherheitstests für Webanwendungen sicherzustellen.
o Setzen Sie Tools wie OWASP ZAP für automatisiertes Scannen ein.
2. NIST: Das Unternehmen würde die NIST-Richtlinien verwenden, um sicherzustellen, dass sein Sicherheitsprogramm insgesamt robust ist. Sie würden:
o Befolgen Sie NIST SP 800–115 zur Strukturierung Ihres Sicherheitstestprozesses.
o Richten Sie Ihre Sicherheitsstrategie am NIST Cybersecurity Framework aus und stellen Sie sicher, dass für alle fünf Kernfunktionen Prozesse vorhanden sind.
3. OSSTMM: Dies würde für eine ganzheitlichere Sicherheitsbewertung verwendet werden. Das Team würde:
o Bewerten Sie die physische Sicherheit Ihrer Rechenzentren mithilfe des Abschnitts zur physischen Sicherheit von OSSTMM.
o Testen Sie die Netzwerksicherheit mithilfe des Abschnitts „Datennetzwerke“.
o Führen Sie Bewertungen des menschlichen Faktors durch, einschließlich Social-Engineering-Tests.
Durch die Kombination dieser Frameworks kann das E-Commerce-Unternehmen eine umfassende Sicherheitsbewertung gewährleisten, die Web-Anwendungen, die allgemeine Cybersicherheitslage sowie spezifische technische und nicht-technische Aspekte ihres Betriebs abdeckt.
Zusammenfassend lässt sich sagen, dass jedes dieser Frameworks seine Stärken hat, sie jedoch häufig am effektivsten sind, wenn sie in Kombination verwendet werden. So können Unternehmen von ihren sich ergänzenden Ansätzen zur Sicherheitsbewertung und -verbesserung profitieren.
4.2 Struktur und Anleitung bereitstellen
Struktur und Anleitung bei Penetrationstests beziehen sich auf standardisierte Frameworks und Methoden, die einen systematischen Ansatz zur Durchführung von Sicherheitsbewertungen bieten. Diese Frameworks bieten mehrere Vorteile:
1. Konsistenz: Stellt sicher, dass alle Aspekte der Sicherheit in jeder Bewertung abgedeckt sind.
2. Effizienz: Bietet Testern einen Fahrplan, an den sie sich halten können, und spart so Zeit und Ressourcen.
3. Vergleichbarkeit: Ermöglicht aussagekräftige Vergleiche zwischen verschiedenen Bewertungen oder über einen bestimmten Zeitraum hinweg.
4. Professionalität: Zeigt einen methodischen Ansatz gegenüber Kunden und Stakeholdern.
Lassen Sie uns drei wichtige Frameworks untersuchen, die Struktur und Anleitung für Penetrationstests bieten:
1. ISSAF (Information Systems Security Assessment Framework)
ISSAF ist ein Open-Source-Framework, das von der Open Information Systems Security Group (OISSG) entwickelt wurde.
Hauptmerkmale:
- Umfassende Abdeckung verschiedener Sicherheitsdomänen
- Detaillierte Methodik für jede Phase des Penetrationstests
- Empfehlungen zu Werkzeugen und Techniken für jeden Schritt
Struktur: ISSAF gliedert sich in drei Hauptphasen:
1. Planung und Vorbereitung
2. Bewertung
3. Meldung, Reinigung und Vernichtung von Artefakten
Praktische Anwendung: Ein großes Finanzinstitut beschließt, eine umfassende Sicherheitsbewertung seiner gesamten IT-Infrastruktur durchzuführen. Aufgrund seines gründlichen Ansatzes wählte es ISSAF.
- In der Planungs- und Vorbereitungsphase definieren sie den Umfang, sammeln Informationen zu ihren Systemen und bereiten Testtools vor.
- Während der Bewertungsphase folgen sie den detaillierten Richtlinien des ISSAF zur Netzwerkkartierung, Schwachstellenidentifizierung und -ausnutzung.
- In der letzten Phase erstellen sie einen detaillierten Bericht über ihre Ergebnisse, bereinigen alle während des Tests vorgenommenen Änderungen und stellen sicher, dass alle gesammelten vertraulichen Daten sicher vernichtet werden.
2. PTES (Durchführungsstandard für Penetrationstests)
PTES bietet eine gemeinsame Sprache und einen gemeinsamen Rahmen für die Durchführung von Penetrationstests.
Hauptmerkmale:
- Sieben Hauptabschnitte, die den gesamten Penetrationstestprozess abdecken
- Technische Richtlinien zur Durchführung von Tests
- Schwerpunkt auf klarer Kommunikation der Ergebnisse
Struktur:
1. Interaktionen vor der Verlobung
2. Informationsbeschaffung
3. Bedrohungsmodellierung
4. Schwachstellenanalyse
5. Ausbeutung
6. Nach der Ausbeutung
7. Berichterstattung
Praktische Anwendung: Ein mittelgroßes E-Commerce-Unternehmen möchte die Sicherheit seines neuen Zahlungsabwicklungssystems testen. Für diese gezielte Bewertung setzt es PTES ein.
- In den Pre-Engagement-Interaktionen definieren Sie den Umfang klar und konzentrieren sich insbesondere auf das Zahlungssystem.
- Während der Informationsbeschaffung und Bedrohungsmodellierung identifizieren sie potenzielle Angreifer und deren wahrscheinliche Methoden.
- Bei der Vulnerability Analysis and Exploitation entdecken und versuchen sie, Schwachstellen im Zahlungssystem auszunutzen.
- Bei der Post-Exploitation geht es darum, zu sehen, wie weit sie sich von einem anfänglich erlangten Zugriff aus bewegen können.
- Abschließend erstellen sie einen ausführlichen Bericht gemäß den PTES-Richtlinien, in dem die Risiken sowohl den technischen als auch den nicht-technischen Beteiligten klar kommuniziert werden.
3. MITRE ATT&CK (Konfrontative Taktiken, Techniken und allgemeines Wissen)
Obwohl es sich bei MITRE ATT&CK strenggenommen nicht um ein Framework für Penetrationstests handelt, bietet es eine umfassende Wissensbasis zu den Taktiken und Techniken der Gegner, die auf Beobachtungen aus der Praxis beruht.
Hauptmerkmale:
- Detaillierte Matrix der Taktiken und Techniken der Angreifer
- Regelmäßige Updates basierend auf der sich entwickelnden Bedrohungslandschaft
- Gilt sowohl für offensive (rotes Team) als auch defensive (blaues Team) Operationen
Struktur: ATT&CK ist in Taktiken (das „Warum“ einer Angriffstechnik) und Techniken (das „Wie“) unterteilt. Es deckt den gesamten Angriffslebenszyklus ab, einschließlich:
- Erster Zugriff
- Ausführung
- Persistenz
- Rechteausweitung
- Verteidigungsausweichmanöver
- Zugangsdaten
- Entdeckung
- Seitliche Bewegung
- Sammlung
- Exfiltration
- Befehl und Kontrolle
Praktische Anwendung: Eine Regierungsbehörde möchte ihre Sicherheitslage gegen Advanced Persistent Threats (APTs) verbessern. Sie integriert MITRE ATT&CK in ihre Sicherheitstests und Verteidigungsstrategien.
- Red Team: Das Penetrationstestteam verwendet ATT&CK, um seine Angriffe zu modellieren und sicherzustellen, dass es Techniken verwendet, die auch von echten Gegnern eingesetzt werden. Beispielsweise könnten sie Techniken verwenden, die unter „Erster Zugriff“ aufgeführt sind, wie Spearphishing oder das Ausnutzen öffentlich zugänglicher Anwendungen.
- Blaues Team: Das Verteidigungsteam verwendet ATT&CK zur Steuerung seiner Erkennungs- und Reaktionsstrategien. Es stellt sicher, dass für jede für seine Umgebung relevante Taktik und Technik Kontrollen und Überwachungen vorhanden sind.
- Berichterstattung: Die Ergebnisse des roten Teams werden der ATT&CK-Matrix zugeordnet und zeigen, welche gegnerischen Techniken erfolgreich waren und welche erkannt oder verhindert wurden.
- Verbesserung: Auf Grundlage der Ergebnisse priorisiert die Agentur Sicherheitsverbesserungen und konzentriert sich dabei auf Bereiche, in denen mehrere ATT&CK-Techniken erfolgreich waren.
Zusammenfassend lässt sich sagen, dass diese Frameworks eine wesentliche Struktur und Anleitung für Penetrationstests bieten und gründlichere, konsistentere und effektivere Sicherheitsbewertungen ermöglichen. Obwohl jedes Framework seine Stärken hat, verwenden viele Organisationen eine Kombination aus Frameworks, um eine umfassende Abdeckung ihrer Sicherheitstestanforderungen zu gewährleisten.
4.3 MITRE ATT&CK
MITRE ATT&CK (Konfrontative Taktiken, Techniken und allgemeines Wissen)
MITRE ATT&CK ist eine weltweit zugängliche Wissensdatenbank zu Taktiken und Techniken der Angreifer, die auf Beobachtungen aus der Praxis basiert. Sie ist als umfassende Matrix des Angreiferverhaltens konzipiert und bietet der Cybersicherheits-Community eine gemeinsame Sprache.
Schlüsselkomponenten:
1. Taktik: Das „Warum“ der Aktion eines Angreifers. Dies sind die taktischen Ziele des Gegners während eines Angriffs.
2. Techniken: Das „Wie“ eines Angriffs. Dabei handelt es sich um die spezifischen Methoden, die Gegner verwenden, um ihre taktischen Ziele zu erreichen.
3. Untertechniken: Spezifischere Beschreibungen des Verhaltens des Gegners als Techniken.
4. Verfahren: Spezifische Implementierungen von Techniken oder Untertechniken, die von Gegnern verwendet werden.
ATT&CK-Matrix: Die ATT&CK-Matrix ordnet Techniken in taktische Kategorien ein:
1. Erster Zugriff
2. Durchführung
3. Beständigkeit
4. Rechteerweiterung
5. Verteidigungsausweichmanöver
6. Zugangsdaten
7. Entdeckung
8. Seitliche Bewegung
9. Abholung
10.Befehl und Kontrolle
11.Exfiltration
12.Auswirkungen
Anwendungsbeispiel:
Betrachten wir ein Penetrationstestszenario für ein Finanzinstitut:
1. Erster Zugriff: Die Penetrationstester könnten einen Spear-Phishing-Angriff (Technik T1566) verwenden, um ersten Zugriff zu erhalten.
2. Ausführung: Sobald sie Zugriff erlangt haben, könnten sie PowerShell (Technik T1059.001) verwenden, um Schadcode auszuführen.
3. Rechteausweitung: Sie könnten eine Schwachstelle zur Rechteausweitung ausnutzen (Technik T1068).
4. Entdeckung: Die Tester könnten Techniken zur Kontoentdeckung (Technik T1087) verwenden, um hochwertige Ziele zu finden.
5. Laterale Bewegung: Sie könnten Remote-Dienste (Technik T1021) verwenden, um sich innerhalb des Netzwerks zu bewegen.
6. Sammlung: Das Team könnte Daten aus lokalen Systemen (Technik T1005) verwenden, um vertrauliche Informationen zu sammeln.
7. Exfiltration: Schließlich könnten sie Daten über ein alternatives Protokoll (Technik T1048) exfiltrieren, um Datendiebstahl zu simulieren.
Szenario aus der realen Welt:
Im Jahr 2019 berichtete FireEye über eine Angriffskampagne, die auf den Versorgungssektor abzielte und die sie „TEMP.Veles“ nannten. Sie verwendeten das MITRE ATT&CK-Framework, um die Aktionen des Angreifers zu beschreiben:
1. Erster Zugriff: Die Angreifer verwendeten Spear-Phishing-E-Mails mit bösartigen Anhängen (Technik T1566.001).
2. Ausführung: Sie nutzten PowerShell-Skripte (Technik T1059.001), um ihre Malware auszuführen.
3. Persistenz: Die Angreifer haben geplante Aufgaben erstellt (Technik T1053.005), um den Zugriff aufrechtzuerhalten.
4. Privilegienerweiterung: Sie nutzten Schwachstellen in ungepatchten Systemen aus (Technik T1068).
5. Umgehung der Verteidigung: Die Angreifer verwendeten verschleierte Dateien (Technik T1027), um einer Entdeckung zu entgehen.
6. Befehl und Kontrolle: Sie verwendeten benutzerdefinierte C2-Protokolle (Technik T1094) zur Kommunikation.
Durch die Zuordnung des Angriffs zu ATT&CK konnte FireEye eine klare und standardisierte Beschreibung des Verhaltens des Bedrohungsakteurs liefern. Dies half anderen Organisationen dabei, ähnliche Angriffe zu verstehen und sich dagegen zu verteidigen.
MITRE ATT&CK und CALDERA:
CALDERA (Cyber Adversary Language and Operations Description for Red Team Automation) ist ein Open-Source-System zur automatisierten Gegneremulation, das von MITRE entwickelt wurde. Es verwendet das ATT&CK-Framework, um Gegneremulationsoperationen durchzuführen.
Die Integration von ATT&CK und CALDERA ermöglicht:
1. Automatisiertes Testen: CALDERA kann Angriffsszenarien basierend auf ATT&CK-Techniken automatisch ausführen.
2. Anpassbare Gegnerprofile: Sicherheitsteams können Profile erstellen, die bestimmte Bedrohungsakteure nachahmen oder bestimmte Angriffsketten testen.
3. Echtzeit-Mapping: Während CALDERA Techniken ausführt, ordnet es sie in Echtzeit der ATT&CK-Matrix zu.
4. Defensive Messung: Organisationen können CALDERA verwenden, um ihre Erkennungs- und Reaktionsmöglichkeiten gegenüber ATT&CK-Techniken zu testen.
Beispiel für kombinierte Nutzung:
Ein großes Unternehmen möchte seine Abwehrmaßnahmen gegen eine bestimmte APT-Gruppe testen. Dabei würde es:
1. Verwenden Sie ATT&CK, um die von dieser APT-Gruppe häufig verwendeten Techniken zu identifizieren.
2. Erstellen Sie basierend auf diesen Techniken ein benutzerdefiniertes Gegnerprofil in CALDERA.
3. Führen Sie automatisierte Tests mit CALDERA durch, das die Techniken auf kontrollierte Weise ausführt.
4. Beobachten Sie, wie ihr Abwehrsystem auf jede Technik reagiert.
5. Nutzen Sie die Ergebnisse, um Ihre Abwehrmaßnahmen zu verbessern, und konzentrieren Sie sich dabei auf Bereiche, in denen die Erkennung oder Prävention fehlgeschlagen ist.
Diese Kombination aus der umfassenden Wissensdatenbank von ATT&CK und den Automatisierungsfunktionen von CALDERA bietet ein leistungsstarkes Tool sowohl für offensive Sicherheitstests als auch für defensive Verbesserungen. Unternehmen können damit ihre Sicherheitslage kontinuierlich und auf kontrollierte, messbare Weise gegen reale Angriffsszenarien testen und verbessern.
4.4 Untersuchung von CVE und CWE
- CVE (Common Vulnerabilities and Exposures): Eine Liste öffentlich bekannter Cybersicherheitsschwachstellen. Jeder Eintrag enthält eine Identifikationsnummer, eine Beschreibung und mindestens eine öffentliche Referenz.
- CWE (Common Weakness Enumeration): Eine von der Community entwickelte Liste von Software- und Hardware-Schwachstellentypen. Sie dient als gemeinsame Sprache zur Beschreibung von Sicherheitsschwächen in Architektur, Design oder Code.
5. Möglichkeiten zur Wahrung der Professionalität beschreiben
5.1 Validierung des Teams
Jedes Mitglied eines PenTesting-Teams muss nachweisen, dass es in einer sicheren Umgebung arbeiten kann:
- Legen Sie Anmeldeinformationen vor: Zum Beispiel relevante Zertifizierungen (z. B. CompTIA PenTest+, CEH), die entsprechende Fähigkeiten zur Durchführung von PenTests nachweisen.
- Führen Sie aktuelle Hintergrundprüfungen durch: Dazu können Kredit-Scores und Fahrausweise gehören. Es ist wichtig sicherzustellen, dass kein Teammitglied vorbestraft ist oder wegen eines Verbrechens verurteilt wurde.
- Betonen Sie, wie wichtig es ist, kriminelle Aktivitäten zu erkennen und zu melden, auch wenn diese Aktivitäten im Zuge der Tests zufällig entdeckt werden.
5.2 Wahrung der Vertraulichkeit
- Alle Mitglieder des PenTest-Teams müssen sich bereit erklären, die Richtlinien zum Umgang mit geschützten und vertraulichen Informationen einzuhalten.
- Das Team sollte dem Kunden ausdrücklich mitteilen, dass die Tester alle Informationen schützen, die sie während des Tests entdecken.
5.3 Vermeidung einer Strafverfolgung
- Vor Beginn der Tests sollte das Team die Vertragsbedingungen detailliert darlegen.
- Überprüfen Sie alle möglicherweise anwendbaren rechtlichen Aspekte.
– Denken Sie sorgfältig alle Szenarien durch, die während des Tests auftreten könnten.
– Gehen Sie Schritt für Schritt durch, wie Sie den Test durchführen und welche Konflikte dabei möglicherweise auftreten.
Abschluss
PenTesting ist ein wichtiges Tool zur Bewertung und Verbesserung der Cybersicherheitslage eines Unternehmens. Durch die Einhaltung etablierter Prozesse, Standards und gesetzlicher Anforderungen können PenTest-Experten ihren Kunden den größtmöglichen Nutzen bieten und gleichzeitig ein Höchstmaß an Professionalität und Ethik wahren.
Dieser umfassende Leitfaden behandelt die wichtigsten Aspekte von Penetrationstests, vom Verständnis der Grundlagen bis zur Einhaltung professioneller Standards. Er bietet eine solide Grundlage für alle, die Penetrationstests in einem organisatorischen Kontext verstehen oder durchführen möchten.
###########################################################
Beispielszenario: PenTest eines E-Commerce-Unternehmens
Unternehmensprofil:
GlobalShop ist ein mittelgroßes E-Commerce-Unternehmen, das weltweit Elektronikartikel verkauft. Das Unternehmen verarbeitet jährlich über 500.000 Kreditkartentransaktionen und speichert Kundendaten wie Namen, Adressen und Kaufhistorie.
Situation:
Der CEO von GlobalShop ist zunehmend besorgt über die Cybersicherheit, nachdem er von den jüngsten spektakulären Datendiebstählen gehört hat. Das Unternehmen beschließt, ein professionelles Penetrationstest-Unternehmen, SecureInsight, mit der Bewertung seiner Sicherheitslage zu beauftragen.
PenTest-Prozess:
1. Planung und Umfang:
SecureInsight trifft sich mit dem IT-Team von GlobalShop, um den Umfang des Tests zu definieren. Sie einigen sich darauf, sich auf die E-Commerce-Plattform, das Zahlungsabwicklungssystem und die Kundendatenbank zu konzentrieren. Sie legen einen Zeitrahmen von zwei Wochen für den Test fest und legen Einsatzregeln fest, darunter eine „Nicht testen“-Liste für kritische Produktionssysteme.
2. Aufklärung:
Das SecureInsight-Team sammelt zunächst öffentlich verfügbare Informationen über GlobalShop. Es ermittelt die IP-Bereiche des Unternehmens, untersucht den Quellcode seiner Website und findet in sozialen Medien mehrere E-Mail-Adressen von Mitarbeitern.
3. Scannen:
Mit Tools wie Nmap durchsucht das Team das Netzwerk von GlobalShop und identifiziert offene Ports und Dienste. Sie entdecken eine veraltete Version von Apache, die auf dem Webserver und mehreren ungepatchten Workstations läuft.
4. Zugang erhalten:
Das Team nutzt eine bekannte Schwachstelle in der veralteten Apache-Version aus und verschafft sich so ersten Zugriff auf den Webserver. Von dort aus führen sie Password-Spraying-Angriffe mit gängigen Passwörtern durch und gelangen so erfolgreich auf ein Administratorkonto.
5. Zugriff aufrechterhalten:
Das Team erstellt auf dem angegriffenen Server eine Hintertür und nutzt diese, um sich seitlich im Netzwerk zu bewegen und schließlich Zugriff auf die Kundendatenbank zu erhalten.
6. Spuren verwischen:
Das Team dokumentiert seine Aktionen sorgfältig und entfernt alle während des Tests erstellten Artefakte, beispielsweise temporäre Dateien oder neue Benutzerkonten.
7. Analyse:
SecureInsight analysiert die Ergebnisse und identifiziert mehrere kritische Schwachstellen:
- Veraltete Serversoftware
- Schwache Passwortrichtlinien
- Unzureichende Netzwerksegmentierung
- Unverschlüsselte Kundendaten
8. Berichterstattung:
Das Team erstellt einen umfassenden Bericht, einschließlich:
- Eine Zusammenfassung für die Führung von GlobalShop
- Detaillierte technische Erkenntnisse
- Risikobewertungen für jede Schwachstelle
- Empfehlungen zur Sanierung
Compliance-Auswirkungen:
- PCI DSS: Der Test zeigt, dass GlobalShop die PCI DSS-Anforderungen nicht vollständig erfüllt, insbesondere in den Bereichen sichere Systeme und Verschlüsselung.
- DSGVO: Das Auffinden unverschlüsselter EU-Kundendaten weist auf mögliche DSGVO-Verstöße hin.
Berufsverhalten:
Während des gesamten Auftrags behandelt SecureInsight seine Ergebnisse streng vertraulich. Außerdem stellt das Unternehmen sicher, dass es innerhalb des vereinbarten Rahmens arbeitet. Es beendet seinen Test, wenn es die Kundendatenbank erreicht, anstatt zu versuchen, Daten zu exfiltrieren.
Ergebnis:
Basierend auf dem Bericht von SecureInsight implementiert GlobalShop mehrere Sicherheitsverbesserungen:
- Aktualisieren der gesamten Serversoftware
- Implementierung strengerer Kennwortrichtlinien und Multi-Faktor-Authentifizierung
- Verbesserung der Netzwerksegmentierung
- Verschlüsselung aller Kundendaten
Sechs Monate später beauftragt GlobalShop SecureInsight mit einem Folgetest, der eine deutliche Verbesserung der Sicherheitslage zeigt.
Dieses Szenario veranschaulicht, wie Penetrationstests in der Praxis funktionieren, und behandelt den Testprozess, Compliance-Überlegungen und professionelles Verhalten. Es zeigt, wie PenTesting echte Schwachstellen identifizieren und zu konkreten Verbesserungen der Cybersicherheit eines Unternehmens führen kann.